Sysinternals Suite
Free Windows Tools for IT Pros
70+ free Windows utilities from Microsoft. Built by Mark Russinovich and maintained since 1996, these are the tools IT pros and developers reach for when Task Manager does not go deep enough.
What Is Sysinternals Suite?
A complete toolkit of Windows system utilities built by Microsoft, used by IT professionals, developers, and security teams around the world.
Sysinternals Suite is a free collection of 70+ Windows diagnostic and administration utilities developed by Mark Russinovich and Bryce Cogswell, and now maintained by Microsoft. Every tool in the package does one thing well: it shows you what is actually happening inside Windows, at a level of detail that built-in tools like Task Manager simply cannot reach.
A Long History, Still Actively Maintained
The project started in 1996 when Russinovich published early tools like NTCrash and NTFSD under the Sysinternals name. Microsoft acquired Sysinternals in 2006, and the toolset has been updated continuously ever since. The March 2026 release bundles all 70+ utilities into a single 167.8 MB ZIP file, making it easy to keep the whole collection at hand without tracking individual downloads.
What the Tools Cover
The suite spans several categories. Process tools like Process Explorer and Process Monitor replace Task Manager and give you real-time visibility into every file access, registry read, and network call a process makes. Network tools like TCPView show every active TCP and UDP endpoint alongside the process that owns it. Security tools like Autoruns expose every program configured to run at startup, across all registry keys and folders Windows checks. Storage tools like SDelete and Disk2vhd handle secure deletion and disk-to-VHD conversion. And utility tools like BgInfo, ZoomIt, and PsExec round out the collection.
Who Uses Sysinternals Suite?
System administrators use it to track down malware, diagnose slow startups, and troubleshoot service failures. Developers use Process Monitor to understand why their application fails on a customer machine when it works fine on their own. Security researchers rely on Sysmon to log detailed system activity to the Windows Event Log. Even everyday power users find tools like Autoruns and BgInfo worth running. Unlike Process Hacker (System Informer) or NirSoft utilities, Sysinternals Suite carries Microsoft’s name directly, which matters in corporate environments where unsigned third-party tools face policy blocks.
Key Features of Sysinternals Suite
Ten essential tools that every Windows power user and IT professional should know. These are not generic monitoring utilities – each one solves a specific class of problem that Windows built-in tools cannot handle.
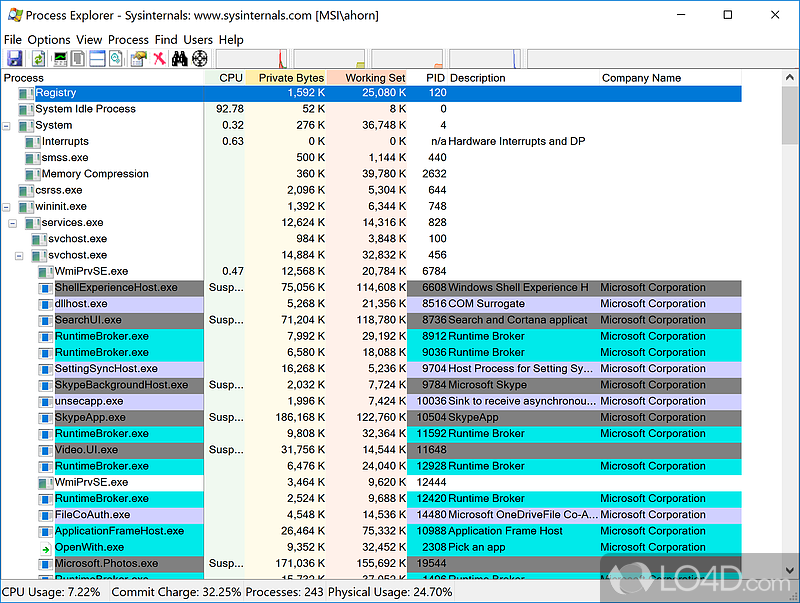
Process Explorer
A far more capable replacement for Task Manager. It shows the full process tree, lists every DLL and handle a process has open, and color-codes processes by type. The VirusTotal integration lets you right-click any process and run its executable hash against 70+ antivirus engines in seconds. When a file is locked by an unknown process, Process Explorer finds it faster than anything else.
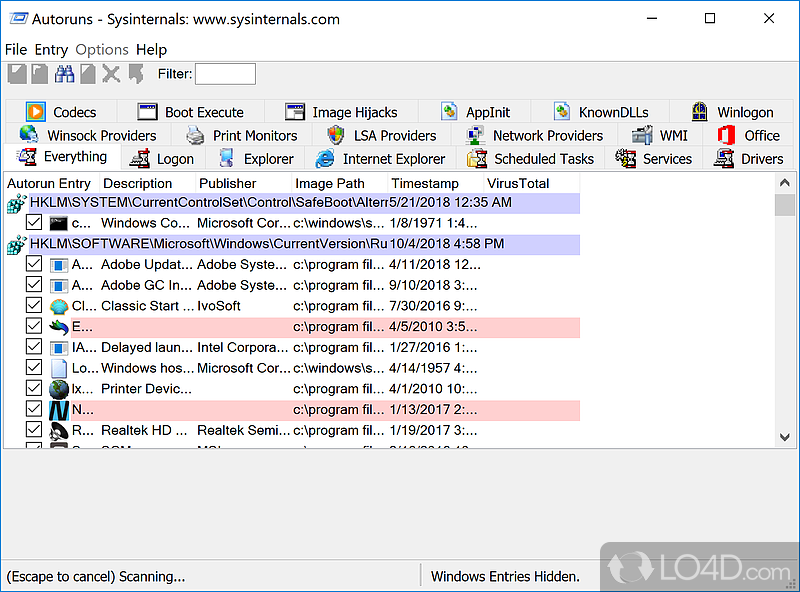
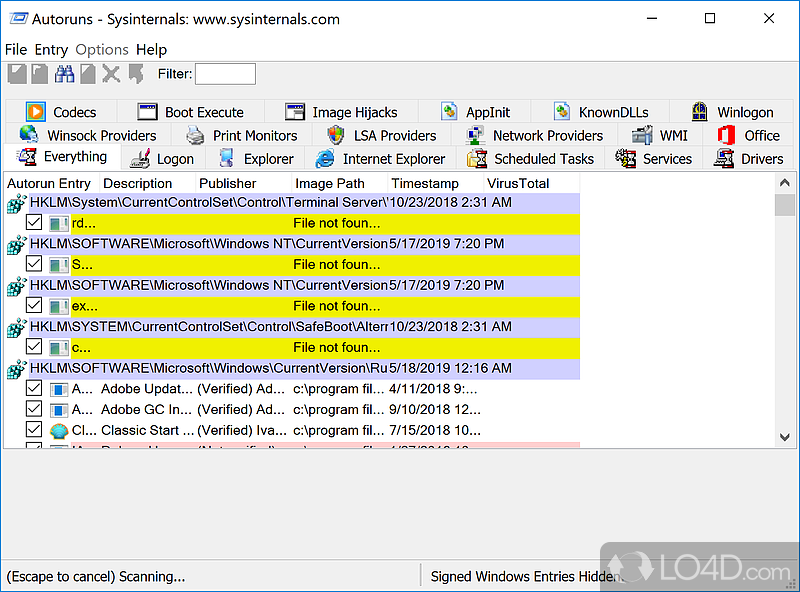
Autoruns
Shows everything configured to run automatically on Windows startup across all autorun locations – far beyond what MSConfig covers. It checks registry Run keys, scheduled tasks, browser extensions, services, drivers, Winlogon entries, and more. Each entry links to its file, and you can disable or delete any item with a checkbox. It is the go-to tool for cleaning up startup bloat and finding persistent malware.
Process Monitor (ProcMon)
Captures every file system read and write, every registry access, and every network connection made by every running process in real time. The event stream can hit millions of entries per minute, but ProcMon’s powerful filter system lets you narrow it to exactly the path, process, or operation you care about. Developers use it to debug “access denied” errors and file-not-found failures that no other tool surfaces.
TCPView
Displays all active TCP and UDP endpoints with the owning process name and PID. It refreshes in real time so you can watch connections open and close as you browse or run applications. Unlike netstat, TCPView shows the process name alongside each connection, not just the PID, and it highlights changes in green and red as connections come and go. Useful for spotting programs phoning home unexpectedly.
PsExec
Runs processes on remote Windows systems over the network without needing to install any client software on the target machine. You can launch a command prompt on a remote PC, run an installer under a different account, or push a script across 50 machines with a single command. IT teams use PsExec for emergency remote administration when RDP is unavailable and for automating tasks across workstation fleets.
Sysmon
A background service that logs detailed system activity to the Windows Event Log – process creation, network connections, file creation, registry modifications, driver loads, and more. Unlike ProcMon’s live-capture approach, Sysmon runs persistently and its logs persist across reboots. Security operations centers (SOCs) deploy Sysmon on every endpoint to feed SIEM platforms like Splunk and Microsoft Sentinel with forensic-quality telemetry.
SDelete
Overwrites files before deleting them so they cannot be recovered by forensic tools. You can securely delete individual files, entire folders, or just wipe the free space on a drive. SDelete follows the Department of Defense 5220.22-M standard, writing multiple passes of random data. This matters when decommissioning a hard drive, preparing a PC for resale, or wiping sensitive data from a system you no longer control.
BgInfo
Writes system information directly onto the desktop wallpaper. By default it shows hostname, IP address, OS version, last boot time, and current user. You configure exactly what appears via a simple GUI, then deploy it via Group Policy to all machines in a domain. In server environments, BgInfo makes it obvious at a glance which machine you are logged into – a simple fix that prevents an entire class of “wrong server” mistakes.
RAMMap
Shows a detailed breakdown of how Windows is using physical memory – which processes have what allocated, how much is in the standby list, and what is sitting in file cache. When a system feels sluggish and Task Manager shows “memory in use” but the suspect applications look normal, RAMMap usually reveals the actual culprit. It can also clear the standby list, which sometimes recovers several gigabytes of RAM instantly without a reboot.
ZoomIt
A screen zoom and annotation tool designed for presentations. Press a hotkey to zoom into any area of the screen, draw arrows and boxes over live content, and type text annotations without leaving the application you are presenting. It has been a fixture in Microsoft conference talks since the early 2000s. The “Break Timer” mode adds a countdown clock overlay, and the “Live Zoom” feature keeps a section of the screen magnified while you type.
System Requirements
Sysinternals tools are native Windows executables with no .NET or runtime dependency. They run on hardware that is 20 years old. Here are the practical requirements for the full suite.
| Component | Minimum | Recommended |
|---|---|---|
| Operating System | Windows 7 SP1, Windows Server 2008 R2 SP1 | Windows 10 22H2 or Windows 11 23H2 (or latest Server 2022) |
| Processor | 1 GHz x86 or x64 processor | 2+ GHz multi-core x64; ARM64 supported via separate ARM64 edition |
| RAM | 256 MB (for individual lightweight tools) | 2 GB+ (Process Monitor captures can consume significant memory) |
| Disk Space | 200 MB for the full Suite ZIP extracted | 500 MB if you plan to save ProcMon capture files (.pml) |
| Display | 800 x 600 resolution | 1920 x 1080 or higher for comfortable use of multi-column tools |
| Permissions | Standard user (some tools work without admin rights) | Local administrator or SeDebugPrivilege for full functionality |
| Internet | Not required – all tools run fully offline | Optional: for VirusTotal integration in Process Explorer and Sigcheck |
| Architecture | x86 (32-bit) – included in full suite ZIP | x64 (64-bit) – separate 64-bit executables included in full ZIP |
Download Sysinternals Suite
Direct download links from Microsoft’s official Sysinternals CDN. No ads, no bundled software, no installer required.
All editions are portable ZIP archives. Extract to any folder and run the tools directly. No setup wizard, no registry changes unless you opt in.
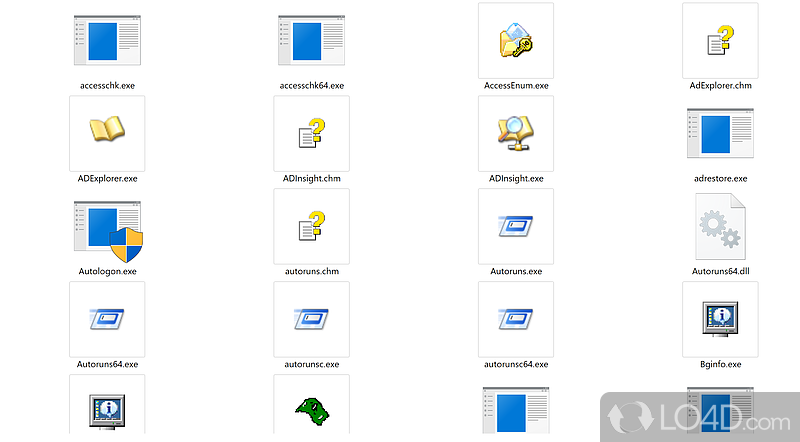
Screenshots
A look at Sysinternals Suite tools in action – from the full file collection to individual utilities like Process Explorer and Autoruns.
Getting Started with Sysinternals Suite
Sysinternals Suite does not have a traditional installer – you extract a ZIP and run tools directly. This guide walks through setup, the most useful tools, and how to get the most out of the collection.
Downloading Sysinternals Suite
Head to the Download section on this page and click the main “Download Sysinternals Suite” button. This links directly to Microsoft’s Sysinternals CDN at download.sysinternals.com, which is the official source. There is no mirror to choose, no sign-in required, and no bundled software in the download.
Three editions are available. The Full Suite (167.8 MB) contains all 70+ tools for standard x86 and x64 Windows and is the right choice for most people. If you are running Windows 11 on an ARM-based device – such as a Snapdragon X Elite laptop or a Surface Pro X – download the ARM64 Edition (15.3 MB) instead for native performance. The Nano Server Edition (9.6 MB) is a stripped-down package for Windows Server Core and Nano Server deployments where the GUI tools are not available.
At 167.8 MB, the full suite takes about 20 seconds on a typical broadband connection. The download is a single ZIP file with no nested archives. If your browser flags the download, that is a generic “downloaded from the internet” warning, not an indication of a problem – these are signed Microsoft binaries.
\\live.sysinternals.com\tools\procexp.exe into Windows Explorer to launch Process Explorer without downloading anything first.Extracting and Setting Up
Sysinternals Suite has no installer. There is no setup wizard, no “Next, Next, Finish” sequence, and nothing written to C:\Program Files automatically. You just extract the ZIP to a folder of your choice and run the tools from there.
The recommended approach is to create a dedicated folder:
- Right-click the downloaded ZIP file and choose Extract All
- Set the destination to
C:\Sysinternals(or any path without spaces) - Click Extract – this creates roughly 170 MB of files including 64-bit versions (procexp64.exe, procmon64.exe, etc.) and their 32-bit counterparts
- Open the folder. You will see a flat list of .exe files, .chm help files, and a few .dll files – no subfolders
To run any tool, simply double-click its .exe. For example, double-click procexp64.exe to open Process Explorer, or autoruns64.exe for Autoruns. Windows may show a SmartScreen warning the first time you run a tool on a fresh Windows installation. This appears because the file was downloaded from the internet, not because the file is dangerous. Click “More info” and then “Run anyway” to proceed – all Sysinternals executables are digitally signed by Microsoft.
Some tools require administrator privileges. If a tool opens briefly and closes, or shows an error about insufficient access, right-click the .exe and choose Run as administrator.
C:\Sysinternals or C:\Tools\Sysinternals so the path stays consistent when you add it to your system PATH variable in Step 3.Initial Configuration
A few one-time setup steps make the whole suite more convenient to use. None are required, but each one saves time daily.
Add Sysinternals to your system PATH so you can launch tools from any command prompt by typing just their name:
- Press Win + R, type
sysdm.cpl, and press Enter - Click the Advanced tab, then Environment Variables
- Under System variables, find and double-click Path
- Click New and type
C:\Sysinternals - Click OK through all dialogs, then open a new Command Prompt and type
procexp
Accept the EULA silently for all tools. Each Sysinternals tool shows a license agreement the first time it runs. To pre-accept all EULAs at once (useful before scripting or deploying), run this from an elevated command prompt:
reg add “HKCU\Software\Sysinternals” /v EulaAccepted /t REG_DWORD /d 1 /fOptional: Install Sysmon for persistent monitoring. Unlike other tools in the suite which you run on demand, Sysmon installs as a Windows service. Run the following from an elevated prompt to install it with default settings:
sysmon64.exe -iSysmon then runs quietly in the background and logs system activity to Applications and Services Logs > Microsoft > Windows > Sysmon in Event Viewer.
sysmon64.exe -i sysmonconfig.xmlYour First Diagnostic Workflow
Here is a practical walkthrough using the two most popular tools – a scenario that comes up constantly in IT and development work: a process is behaving strangely, and you need to find out what it is doing and why.
Step 1 – Open Process Explorer (procexp64.exe as admin). The main window shows a color-coded tree of all processes. Purple rows are image-packed executables (potentially suspicious). Green rows are newly-created processes. You can hover over any process to see its full path, command-line arguments, and company name. Right-click any process and choose Properties to see its loaded DLLs, open handles, threads, and performance counters.
Step 2 – Check the process against VirusTotal. Right-click any suspicious process and choose Check VirusTotal.com. Process Explorer hashes the executable and queries VirusTotal’s API, showing the detection count (e.g., “0/72” means clean, “15/72” means concern) directly in the list. This takes about 5 seconds and requires internet access.
Step 3 – Capture what the process is doing with Process Monitor (procmon64.exe as admin). Press Ctrl + E to start capturing, then reproduce the behavior you are investigating. Press Ctrl + E again to stop. Now set a filter: go to Filter > Filter, set Process Name is [your process].exe, click Add, then OK. The list now shows every file read, registry access, and network call that process made.
Common filter for “file not found” errors: Add a second filter: Result is NAME NOT FOUND. This shows every path the process tried to open that did not exist – often revealing exactly which missing file or registry key is causing the failure.
| Tool | Shortcut | Action |
|---|---|---|
| Process Explorer | Ctrl + H | Switch to handle view |
| Process Explorer | Ctrl + D | Switch to DLL view |
| Process Explorer | Ctrl + F | Find handle or DLL |
| Process Monitor | Ctrl + E | Start / stop capture |
| Process Monitor | Ctrl + L | Open filter dialog |
| Process Monitor | Ctrl + X | Clear display |
| Autoruns | F5 | Refresh all entries |
| ZoomIt | Ctrl + 1 | Enter zoom mode |
Tips, Tricks, and Best Practices
Keep the suite up to date. Sysinternals tools are updated whenever Windows internals change. There is no auto-updater – the simplest approach is to re-download the full suite ZIP every few months and overwrite your existing folder. You can check the latest release date at learn.microsoft.com/en-us/sysinternals/downloads/sysinternals-suite.
Use Autoruns before installing new software. Take a snapshot before and after installing any application to see exactly what it added to your startup. In Autoruns, go to File > Save before installation, then File > Compare after to highlight every change the installer made.
Run PsExec with caution in corporate environments. Because PsExec is commonly abused in ransomware attacks, many EDR solutions flag it. If you use it legitimately, coordinate with your security team to whitelist it by hash rather than name, since attackers often rename it.
Use SDelete before selling or repurposing drives. A single-pass wipe is enough for modern HDDs and SSDs – multiple passes add time without improving security. The command sdelete64 -z C: zeroes free space, which is the standard approach for preparing a drive image for distribution.
Resources for going deeper:
- Microsoft Learn – Official documentation at learn.microsoft.com/en-us/sysinternals/
- r/sysadmin and r/netsec – Active communities where real-world ProcMon and Autoruns findings get shared
- “Troubleshooting with Sysinternals” – Mark Russinovich’s own conference talks, available on the Microsoft Learn YouTube channel
- Windows Internals (book) – Covers the OS concepts behind what these tools show
Frequently Asked Questions
Common questions about downloading, using, and troubleshooting Sysinternals Suite.
Is Sysinternals Suite free to download?
Yes, Sysinternals Suite is completely free. Microsoft makes all 70+ tools available at no cost, with no subscription tier, no feature unlock, and no “premium” version. The suite has been free since it was part of the original Sysinternals website in the late 1990s, and Microsoft has maintained that pricing policy since acquiring the company in 2006.
The download is a direct ZIP file from Microsoft’s own CDN at download.sysinternals.com. There is no registration, no email address required, and no download manager to install. The full suite (167.8 MB) and the ARM64 edition (15.3 MB) are both available without any account. Individual tools are also available as standalone downloads from the Microsoft Learn Sysinternals documentation pages.
There are no license fees for personal or commercial use. Many organizations deploy Sysinternals tools across entire fleets of workstations for IT administration and security monitoring. The license agreement (which you must accept the first time you run each tool) permits use within your organization – you cannot redistribute the tools commercially or strip the Microsoft branding.
Pro tip: If you need to pre-accept the EULA across a managed deployment, you can push a registry key: HKCU\Software\Sysinternals\EulaAccepted = 1 via Group Policy before your users first launch the tools.
See the Download section above for direct download links.
Is Sysinternals Suite safe for Windows 11?
Yes, Sysinternals Suite is safe for Windows 11. Every executable in the suite is digitally signed by Microsoft Corporation, so Windows can verify the publisher before running the tool. Antivirus vendors who flag Sysinternals tools are almost always triggering on behavioral heuristics – PsExec looks like remote-access malware, ProcMon hooks the kernel like a rootkit – not on any malicious code in the files themselves.
The latest release (March 26, 2026) was built and tested on Windows 11. Tools like Process Explorer, Autoruns, and Process Monitor work correctly on Windows 11 22H2 and 23H2 including the ARM64 builds for Snapdragon X Series devices. The dark mode introduced in 2022 integrates with Windows 11’s system-wide dark theme setting.
If Windows Defender or your endpoint security platform flags a Sysinternals tool, here is how to handle it:
- Verify the file is signed by Microsoft: right-click the .exe, Properties, Digital Signatures tab
- Check the file hash against the current official download – re-download if you are unsure about the source
- Add a hash-based exclusion in your security software for the specific tool you need
- Do not create broad folder exclusions for C:\Sysinternals – use per-file hash rules instead
Pro tip: You can verify any Sysinternals tool’s signature from the command line with the included Sigcheck tool: sigcheck64.exe -v procexp64.exe – it checks both the file signature and VirusTotal simultaneously.
Check System Requirements for the full compatibility matrix.
Does Sysinternals Suite require installation?
No, Sysinternals Suite does not require installation. The entire suite ships as a ZIP file. You extract it to any folder, and every tool runs directly as a portable .exe. Nothing is written to C:\Program Files, no entries are added to the registry (unless you run Sysmon, which installs as a service by choice), and there is no uninstaller because there is nothing to uninstall.
The portable nature of the tools is one of their most useful properties. You can carry the suite on a USB drive and run it on any Windows machine without touching the system. IT professionals often keep the suite on a bootable diagnostic drive or a shared network folder accessible from any workstation. You can also run tools directly from a UNC path or a network share.
The exception is Sysmon, which must be explicitly installed as a Windows service if you want persistent logging. To install it: sysmon64.exe -i [optional: -c config.xml]. To uninstall it later: sysmon64.exe -u. The other 70+ tools in the suite have no installation step at all.
Some tools create small per-user settings files in the user profile (for example, Process Monitor saves its filter settings to a .pmc file) but these are optional and stored in your user AppData folder, not in system locations.
Pro tip: Create a folder at C:\Sysinternals and add it to your system PATH variable. Then you can type procexp or autoruns in any command prompt or the Run dialog to launch tools instantly without navigating to the folder.
See the Getting Started section for step-by-step extraction and PATH setup instructions.
What tools are included in Sysinternals Suite?
Sysinternals Suite bundles 70+ individual Windows utilities. The most widely used ones fall into five categories: process management, network monitoring, security and diagnostics, disk and file utilities, and system information tools.
The most commonly used tools by category:
- Processes: Process Explorer, Process Monitor (ProcMon), ProcDump, ListDLLs, Handle
- Network: TCPView, Whois, PsPing
- Security & Startup: Autoruns, Sigcheck, Sysmon, AccessChk, AccessEnum, ShareEnum
- Disk & Files: Disk2vhd, DiskView, Du (disk usage), SDelete, NTFSInfo, PageDefrag
- System Info: BgInfo, RAMMap, VMMap, CoreInfo, ClockRes, WinObj, LoadOrder
- Remote Admin (PsTools): PsExec, PsInfo, PsKill, PsList, PsLoggedOn, PsService, PsShutdown, PsLogList
- Utilities: ZoomIt, RDCMan, BGInfo, DebugView, RegJump, Strings, Streams
Both 32-bit and 64-bit versions of each tool are included in the full suite ZIP (e.g., procexp.exe and procexp64.exe). On 64-bit Windows, always use the 64-bit variants for accurate results – the 32-bit versions of some tools cannot see 64-bit processes correctly.
Pro tip: The .chm help file included with each tool (e.g., procexp.chm) contains complete documentation with screenshots. Right-click the .chm file and choose Properties, then click Unblock if Windows has blocked it from opening.
See the Key Features section for detailed descriptions of the 10 most essential tools.
What are the system requirements for Sysinternals Suite?
Sysinternals Suite runs on Windows 7 SP1 and later, including Windows 10, Windows 11, and all Windows Server versions from 2008 R2 onwards. The tools are native Windows executables with no .NET Framework requirement, which means they start quickly and work on even heavily locked-down enterprise images.
Hardware requirements are minimal. A 1 GHz processor and 256 MB of RAM will run most tools without issues. The one tool that can be demanding is Process Monitor in high-throughput scenarios – when capturing events from a busy system, ProcMon’s buffer can consume several gigabytes of RAM if you let it run for hours without clearing. For normal diagnostic sessions (minutes rather than hours), 1 GB of RAM is plenty.
Disk space is 167.8 MB for the full suite ZIP extracted. If you routinely save Process Monitor capture files (.pml files), allocate extra space – a 10-minute capture on a busy system can produce a 500 MB+ file.
Architecture coverage:
- x86 (32-bit Windows): Included in the full suite ZIP
- x64 (64-bit Windows): Included in the full suite ZIP (use procexp64.exe etc.)
- ARM64 (Windows 11 on ARM): Separate ARM64 edition download (15.3 MB)
- Nano Server: Separate Nano Server edition (9.6 MB) – GUI tools excluded
Pro tip: Most GUI tools require Local Administrator rights or SeDebugPrivilege. If you need to run diagnostics as a standard user, use AccessChk to check what access the standard user account has before escalating.
Full details are in the System Requirements table above.
Why does Windows SmartScreen warn when running Sysinternals tools?
Windows SmartScreen shows a warning because the executable was downloaded from the internet and has not yet built up enough “reputation” on your specific machine. This is a generic internet-download warning that triggers for any program you download, not a specific flag against Sysinternals tools.
The important distinction: SmartScreen can warn about files that are simply new downloads, or it can warn about files it believes are malicious. For Sysinternals tools, the warning is always the former – the tools are digitally signed by Microsoft Corporation, which you can verify by right-clicking the .exe, choosing Properties, and checking the Digital Signatures tab.
To dismiss the warning and run the tool:
- When SmartScreen appears, click “More info” (small text, left side)
- A “Run anyway” button will appear – click it
- You will only see this warning once per tool per machine
Alternatively, right-click the .exe file, choose Properties, and click the Unblock checkbox at the bottom of the General tab. This removes the “Zone.Identifier” alternate data stream that marks the file as downloaded from the internet, which is what triggers SmartScreen in the first place.
To unblock all tools at once, run from an elevated PowerShell: Get-ChildItem C:\Sysinternals -Recurse | Unblock-File
Pro tip: If you are deploying Sysinternals tools via Group Policy or SCCM, use a software distribution method that does not attach the Zone.Identifier stream – files deployed via Group Policy Preferences or SCCM packages do not trigger SmartScreen warnings.
See also: Getting Started Step 2 for more about the first-run experience.
Does Sysinternals Suite work on Windows 10?
Yes, all Sysinternals tools work on Windows 10, including the latest 22H2 build. Windows 10 is the most tested platform for the suite, and Microsoft regularly validates the tools against Windows 10 feature updates before releasing new versions. Tools like Process Explorer, Autoruns, ProcMon, and TCPView behave identically on Windows 10 and Windows 11.
A few Windows 10-specific notes worth knowing:
- Dark mode support arrived in October 2022, so the GUI tools respect Windows 10’s system-wide light/dark theme setting if you are on that version or later.
- Process Explorer on Windows 10 shows UWP (Universal Windows Platform) apps and their container processes, which look different from Win32 processes in the tree.
- Autoruns on Windows 10 includes entries for scheduled tasks and UWP autostart registrations that older Windows versions did not have.
- Sysmon on Windows 10 can log DNS query events (Event ID 22) and clipboard capture events (Event ID 24), both of which require Windows 10 build 1709 or later.
If you are on Windows 10 32-bit (still used on some older hardware), use the 32-bit versions of each tool (e.g., procexp.exe rather than procexp64.exe). On 64-bit Windows 10, always use the 64-bit variants for complete visibility.
Pro tip: Windows 10 ships with a built-in package manager (winget) that can download and update many tools, but Sysinternals Suite is not in the winget repository. Download it directly from the Download section or use the Sysinternals Live network share.
How do I update Sysinternals Suite to the latest version?
Sysinternals Suite has no built-in auto-updater. To update, you download the latest ZIP from the Download section and extract it over your existing Sysinternals folder, overwriting the old files. The entire process takes about two minutes.
Steps to update:
- Close any running Sysinternals tools (so their .exe files are not locked)
- Download the latest SysinternalsSuite.zip from the Download section on this page
- Extract the ZIP to the same folder where your current tools live (e.g.,
C:\Sysinternals) - Choose “Replace all files” when Windows asks about overwriting
- Relaunch any tools you need – they will be the updated versions
Individual tools can also be updated independently. Each tool has its own page on Microsoft Learn (e.g., learn.microsoft.com/en-us/sysinternals/downloads/procexp) where you can see its release date and download just that tool as a standalone ZIP.
Microsoft typically updates individual tools on an as-needed basis – when a Windows update changes system internals that affect the tool – rather than on a fixed schedule. The full suite bundle is updated roughly monthly to reflect the latest individual tool releases. You can see the exact date on the Sysinternals Suite download page.
Pro tip: Create a scheduled task or a simple PowerShell script that downloads the ZIP, extracts it, and verifies the version – this is the closest thing to auto-update the suite offers. Run it monthly or after major Windows feature updates to stay current.
To check the current version of a specific tool, right-click its .exe and choose Properties, then click the Details tab to see the file version number.
Does Sysinternals Suite work on Mac or Linux?
Most Sysinternals tools are Windows-only. The suite was built specifically for Windows internals and has no macOS version. However, Microsoft has ported a handful of tools to Linux as standalone open-source releases.
Available on Linux (from Microsoft GitHub):
- ProcMon for Linux – Process Monitor ported to Linux, available as an AppImage and .deb package from github.com/Microsoft/ProcMon-for-Linux. It monitors file system events using eBPF and produces output in a format similar to the Windows version.
- ProcDump for Linux – Dumps a process on trigger conditions (CPU spike, memory threshold, signal). Available from github.com/Microsoft/ProcDump-for-Linux.
On macOS, there are no official Sysinternals ports. Mac users working on Windows diagnostics typically run the tools in a Windows virtual machine (VMware Fusion, Parallels, or the free UTM). For native macOS alternatives with similar functionality: Activity Monitor covers basic Process Explorer use cases, fs_usage approximates Process Monitor’s file monitoring, and Little Snitch or Lulu cover network monitoring similar to TCPView.
On Windows Subsystem for Linux (WSL 2), Process Monitor for Linux can run inside the WSL environment to monitor Linux processes, while Windows-side tools like Process Explorer can monitor the WSL host process (vmmem) from the Windows side.
Pro tip: For cross-platform IT shops, Sysmon for Linux (github.com/Microsoft/SysmonForLinux) provides the same event log telemetry as Windows Sysmon, making it possible to correlate Windows and Linux system events in the same SIEM with a consistent event schema.
For Windows downloads, see the Download section above.
What is Sysinternals Live and how does it work?
Sysinternals Live is a network share hosted by Microsoft that lets you run any Sysinternals tool directly over the internet without downloading it first. You access it via the UNC path \\live.sysinternals.com\tools\ from Windows Explorer or from a Run dialog.
To use it, open File Explorer and type \\live.sysinternals.com\tools\ in the address bar. Windows mounts the network share and shows all 70+ tool executables as if they were local files. Double-click any tool to run it – Windows streams the executable and launches it. You can also run tools directly from the command line: \\live.sysinternals.com\tools\procexp.exe
Practical use cases:
- Diagnosing a machine you cannot copy files to (locked-down endpoint, no USB access)
- Running a quick check without permanently installing tools on a system
- Always getting the latest version of a tool without maintaining a local copy
The limitations: it requires internet access (obviously), the tool download happens at startup which adds 2-5 seconds per launch depending on your connection, and some tools are blocked by corporate firewalls that deny WebDAV or SMB access to external hosts. The EULA acceptance still applies – the first run of each tool on each machine will show the license agreement.
Pro tip: You can map Sysinternals Live as a network drive for easy access: net use S: \\live.sysinternals.com\tools. Then type S:\procexp.exe to launch Process Explorer from anywhere on that machine.
For offline environments, download the full suite from the Download section instead.
Can I use Sysinternals Suite offline without internet access?
Yes, Sysinternals Suite works fully offline. The tools are self-contained native Windows executables that do not need internet access to run. You download the ZIP once, extract it, and every tool in the suite runs without any network connection.
The only features that require internet access are:
- VirusTotal integration in Process Explorer and Sigcheck – these query VirusTotal’s API with a file hash. Without internet, the VirusTotal column simply shows no result.
- Sysinternals Live (
\\live.sysinternals.com) – which is the online-only delivery method, not the downloaded suite. - Update checking – no built-in auto-update, but if you have an update checker script it needs internet to check for new versions.
In air-gapped or restricted corporate environments, the downloaded suite works exactly as expected. Process Monitor captures kernel events locally, Autoruns reads the local registry and file system, TCPView monitors local network state, Sysmon logs to the local Windows Event Log. All core functionality is entirely local.
For environments where even the initial download is controlled, your IT administrator can push the Sysinternals tools via SCCM, Intune, or a software distribution package without individual machines ever accessing the Microsoft CDN directly.
Pro tip: ProcMon capture files (.pml) can be collected from offline machines and then opened for analysis on a different machine that has internet access, letting you do VirusTotal lookups and remote analysis without needing to connect the target machine to the internet.
Download the full offline-ready suite from the Download section above.
Sysinternals Suite vs Process Hacker – which is better?
Both are excellent, and many professionals use both. The honest answer is that they solve different problems well, and the “better” tool depends on exactly what you are trying to do.
Sysinternals Suite wins on breadth. You get 70+ tools covering far more ground than Process Hacker’s single executable – Autoruns alone does something Process Hacker does not touch. The tools carry Microsoft’s signature, which matters in corporate environments where unsigned tools face execution policy blocks. Sysinternals is also actively maintained by a team at Microsoft that understands Windows internals deeply, and the documentation is excellent.
Process Hacker (now rebranded System Informer) wins on depth within its process monitoring scope. Its network tab, service management, and memory editor are more capable than Process Explorer in some specific scenarios. The open-source nature means the community can fix issues and add features between official releases. System Informer supports custom plugins and has a more configurable UI.
Key practical differences:
- Startup management: Autoruns (Sysinternals) is far better – Process Hacker has no equivalent
- Live process view: Very similar capability; System Informer has a slightly more detailed network tab
- Enterprise deployment: Sysinternals is easier – signed by Microsoft, no policy issues
- Remote administration: Sysinternals wins with PsExec, PsInfo, and the full PsTools suite
- Security logging: Sysmon (Sysinternals) has no equivalent in Process Hacker
- NirSoft Utilities is a third option that fills gaps both leave – particularly for password recovery and network tools
Pro tip: Install both on your diagnostic toolkit. Use Sysinternals for startup management, remote admin, and security monitoring; use System Informer when you need deep process inspection and memory editing. They do not conflict.
Download Sysinternals Suite from the Download section above.
How do I run Sysinternals tools as administrator?
Most Sysinternals tools require administrator privileges for full functionality. The standard way to run a tool as admin is to right-click its .exe and choose “Run as administrator.” Windows will show a UAC prompt if your account is not already elevated.
Three approaches for running tools with admin rights:
- Right-click method: Right-click the .exe file and choose “Run as administrator” – UAC prompts for confirmation. This is the simplest one-time approach.
- Compatibility settings: Right-click the .exe, Properties, Compatibility tab, check “Run this program as an administrator.” The tool will always prompt for UAC when launched.
- Elevated command prompt: Open a Command Prompt as administrator (right-click Start, “Terminal (Admin)” or “Command Prompt (Admin)”), then navigate to your Sysinternals folder and run tools from there. Any tool you launch from an elevated prompt inherits admin rights.
On systems where your user account does not have local admin rights, you will need to use runas /user:DOMAIN\Administrator procexp64.exe and enter the administrator password when prompted.
In a domain environment, IT staff sometimes run Sysinternals tools on remote machines via PsExec: psexec64.exe \\TARGETPC -s procexp64.exe – the -s flag runs it as the SYSTEM account, which has even higher privileges than local admin.
Pro tip: Some tools like BgInfo and ZoomIt work perfectly without admin rights. Only tools that inspect kernel structures (Process Explorer, Process Monitor, Autoruns) need elevation for their core functionality. If a tool opens briefly and closes or shows an “access denied” error, try running it as administrator first before troubleshooting further.
See the Getting Started guide for more setup tips.
How do I add Sysinternals to the Windows PATH?
Adding Sysinternals to your Windows PATH lets you launch any tool by typing its name in any Command Prompt, PowerShell window, or the Run dialog (Win + R) – no need to navigate to the folder each time.
Steps to add Sysinternals to PATH (Windows 10 and 11):
- Press Win + R, type
sysdm.cpl, press Enter to open System Properties - Click the Advanced tab, then Environment Variables
- Under “System variables” (bottom section), find the variable named Path and double-click it
- In the Edit Environment Variable dialog, click New
- Type
C:\Sysinternals(or whichever folder you extracted the tools to) - Click OK through all three dialogs
- Open a new Command Prompt (the PATH change does not apply to already-open windows)
- Type
procexpand press Enter – Process Explorer should launch
Alternatively, from an elevated PowerShell in one line:
[Environment]::SetEnvironmentVariable(“Path”, $env:Path + “;C:\Sysinternals”, “Machine”)Once PATH is set, you can run any tool by name. For example: type autoruns to open Autoruns, procmon for Process Monitor, tcpview for TCPView, or bginfo for BgInfo. Tab completion in PowerShell also works for tool names.
Pro tip: Add both C:\Sysinternals to the System PATH (for all users) and separately, if you have PsTools you want available, the same folder covers them too since all tools are in one flat directory. For 64-bit systems, tools like procexp64, procmon64 and autoruns64 are the ones to run – the PATH lets you call them by the 64-bit name directly.
See Getting Started Step 3 for full initial setup instructions.
How do I uninstall Sysinternals Suite?
Uninstalling Sysinternals Suite is straightforward because there is no installation process – you simply delete the folder you extracted the tools to. There is no entry in “Add or Remove Programs” because nothing was installed via an installer.
Complete cleanup steps:
- Delete the Sysinternals folder (e.g.,
C:\Sysinternals) – this removes all 70+ tools - Remove the PATH entry: Go to System Properties (Win + R,
sysdm.cpl), Advanced, Environment Variables, find Path under System variables, and delete the Sysinternals entry - Remove saved settings (optional): Process Monitor saves filters to
%APPDATA%\Roaming\Sysinternals\– delete this folder if you want a complete cleanup - Remove EULA registry keys (optional): Delete
HKCU\Software\Sysinternalsfrom the registry via regedit if you want to remove all traces - Uninstall Sysmon if you installed it: From an elevated command prompt, run
sysmon64.exe -ubefore deleting the files. If you delete sysmon64.exe before uninstalling the service, usesc delete Sysmon64to remove the service entry manually.
The suite leaves no background services running (except Sysmon if you chose to install it), no registry entries for startup (unless you created them), and no scheduled tasks. After deleting the folder, the suite is fully gone from the system.
Pro tip: If you want to temporarily remove the tools from a system without permanently deleting them, simply remove the folder from PATH. The files remain on disk, but no processes can launch them accidentally, and they will not show up in application searches.
Need to start fresh? Download the latest suite from the Download section above.
What is the best Sysinternals tool for beginners?
For someone just starting with Sysinternals, Autoruns is the best first tool to learn. It has a practical immediate use case (cleaning up slow startups), its UI is self-explanatory compared to Process Monitor’s event flood, and you can learn it in 10 minutes and see real results right away.
The beginner toolkit, in order of learning priority:
- Autoruns – Launch it, let it scan, look at the “Logon” and “Scheduled Tasks” tabs. Anything you do not recognize, right-click and choose “Search Online.” Uncheck entries you want to disable (they stay in the list, just disabled – you can re-enable if something breaks). This alone can speed up boot times measurably.
- Process Explorer – Replace Task Manager permanently: go to Options > Replace Task Manager. Learn to read the process tree colors: cyan = service, purple = packed executable (flag this for review), green = new process. Right-click any process to search online or check VirusTotal.
- TCPView – Open it and watch network connections in real time. The color changes (green = new connection, red = closed connection) make it easy to spot which programs are connecting to where.
Save Process Monitor for when you have a specific problem to debug – it generates overwhelming amounts of data until you know how to filter it. Beginners who start with ProcMon often get discouraged by the volume. Start with Autoruns, graduate to Process Explorer, and learn ProcMon once you have a specific question to answer.
Pro tip: The best way to learn Process Explorer is to open it alongside your regular work for a week without changing anything. Just observe the process tree, learn what normal looks like on your system, and notice when new processes appear. After a week, abnormal processes will be immediately obvious.
Download Sysinternals Suite from the Download section and follow the Getting Started guide for setup.
Where is the official download for Sysinternals Suite?
The official source for Sysinternals Suite is Microsoft’s own Sysinternals download CDN at download.sysinternals.com. The direct download URL for the full suite is https://download.sysinternals.com/files/SysinternalsSuite.zip, which always points to the current release.
The official documentation and per-tool download pages are at learn.microsoft.com/en-us/sysinternals/, where you can also find changelogs, release notes for each tool, and the complete documentation library.
If you want to verify you have the genuine files:
- Download from the Download section on this page or directly from download.sysinternals.com
- After downloading, right-click any .exe, choose Properties, click Digital Signatures – the signer should be Microsoft Corporation
- The Authenticode timestamp on the signature confirms when the file was signed – current releases were signed in early 2026
Avoid downloading Sysinternals tools from unofficial mirrors or file-sharing sites. Because these tools touch sensitive parts of the OS (processes, memory, network), fake or modified versions are a real risk. Always verify the Microsoft signature before running any tool.
The suite is also available from the Microsoft Store for Windows (Product ID: 9p7knl5rwt25), which provides an alternative delivery method for environments where store deployments are preferred. However, the direct ZIP download from Microsoft’s CDN is the fastest and most reliable option for most use cases.
Pro tip: Bookmark the Download section for fast access to the latest direct links whenever a new version releases.
